Difference between revisions of "Grid certificates"
| Line 1: | Line 1: | ||
| − | [[Category:Grid]] | + | [[Category:Grid computing]] |
[[Getting started with SweGrid|< Getting started with SweGrid]] | [[Getting started with SweGrid|< Getting started with SweGrid]] | ||
Revision as of 13:20, 8 July 2011
< Getting started with SweGrid
A certificate is the equivalent of a passport in real-life. In the same way you have prove your credentials when you aquire a passport the same is true for a certificate. A Certificate Authority (CA) has to vouch for your identity and sign your certificate.
A certificate consist of 2 parts a private key and a public key. The private is your secret and should be kept as secure as possible. The public key is used to verify signatures are signed with your private key for the receiving part. The public part is also used to verify that the certficate is correct when you have the public part of the CA certificate.
For more information regarding certificates and public key cryptography:
http://en.wikipedia.org/wiki/Public-key_cryptography
http://en.wikipedia.org/wiki/Public_key_certificate
http://www.nordugrid.org/documents/certificate_howto.html
Contents
Requesting a certificate
Requesting a certificate using the Terena eScience Portal
The Terena eScience Portal is a joint effort to provide users with a tool for requesting grid-certificate with the credentials from their home-institution or university.
To request a Terena eScience Certificate go to the following URL:
https://tcs-escience-portal.terena.org
The procedure is as follows:
1. Click "Login" 2. Click on Sweden in the map. 3. Choose your identity provider in the drop down box. 4. Login using your credentials from your identity provider.
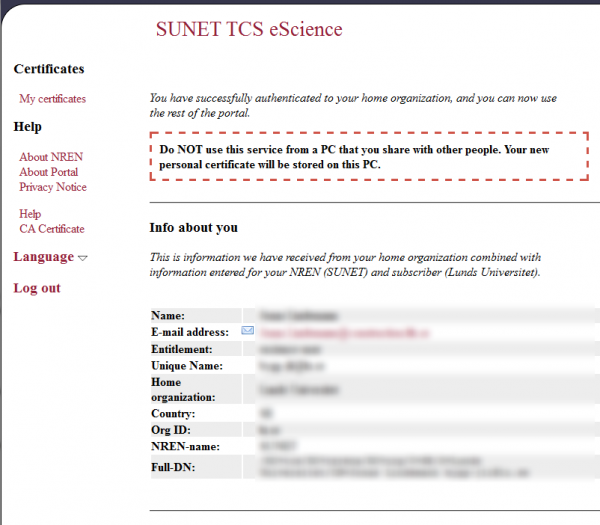
You should now arrive to a "home" page that shown below:
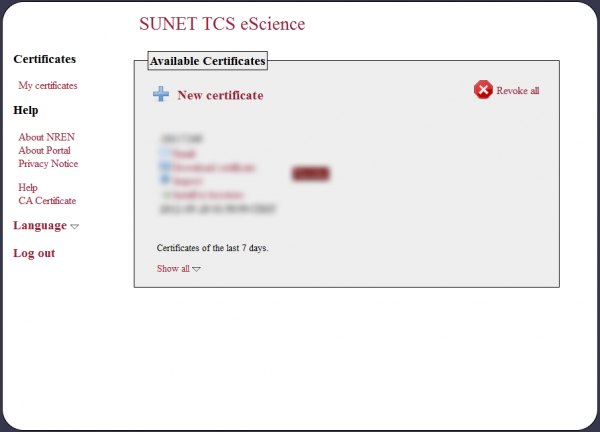
5. Click on the "My certificates" link in the top left side of the page. You should then arrive to a page from which you will create and manage your certificates.
6. To create a new certificate, click on the "New certificate" link and follow the instructions. When the process is completed your certificate will be listed on the same page.
7. Install the signed certificate in your browser by clicking on the "Install in keystore" link. This will install the certificate in the key-store of your browser.
Exporting Terena certificate for use with Grid tools
To use the Terena certificates with the ARC grid client they have to be exported from the browser and converted into a suitable format. To export and convert a certificate installed the following procedure can be used:
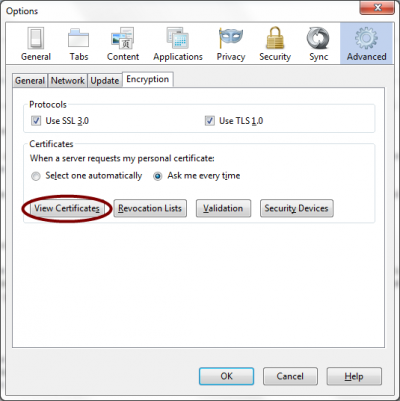
1. Export the installed certificate from the browser in the PKCS12 format. In Firefox this is accomplished from the Options/Advanced/Encryption Dialog, shown below:
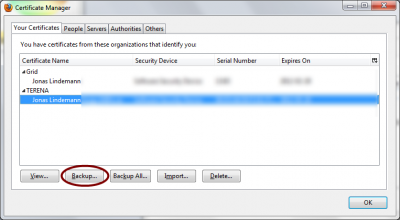
To show all installed certificate click on the "View Certificates" buttton. This will shown the following dialog:
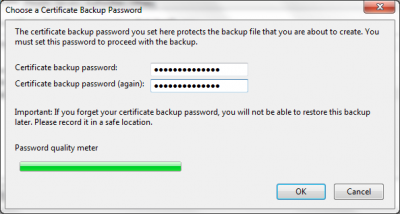
To backup your newly created certificate select the Terena certificate and click on the "Backup" button in the previous dialog. This brings up a dialog for selecting a filename and location for the certificate. Save your certificate in a good location. The file with be given the extension .p12 indicating that it is a PKCS12 certificate. When the location has been selected another dialog is shown asking for a export password. This password will protect the certificate and private key. As show in the next figure:
Use the password quality meter to choose a strong password for the exported certificate and private key.
2. Converting the PKCS12 certificate to a format suitable for use with grid clients (PEM)
Create a directory, .globus, in your home directory.
Linux / Unix:
$ cd ~ $ mkdir .globus $ cd .globus
In windows
C:\...\>cd C:\Users\<username> C:\...\>mkdir .globus C:\...\>cd .globus
Using the "openssl" command we now convert the exported certifcate to the correct format. Windows users: OpenSSL for Windows is available here.
The first step is to convert the private key. The openssl command will first ask for the password chosen when the certificate was exported ("Enter Import Password:"). In the next step the pass phrase for the exported private key is chosen ("Enter PEM pass phrase:"). Please choose a strong passphrase.
openssl pkcs12 -nocerts -in usercert.p12 -out userkey.pem Enter Import Password: MAC verified OK Enter PEM pass phrase: Verifying - Enter PEM pass phrase:
In the next step the certificate is converted. In the same way as with the private key we have to specify the export password again ("Enter Import Password:").
openssl pkcs12 -clcerts -nokeys -in usercert.p12 -out usercert.pem Enter Import Password: MAC verified OK
Before we can use the private key with or client tools the permissions on the private key file (userkey.pem) has to changed to a more restrictive setting (Linux/Unix):
chmod 400 userkey.pem
Requesting a certificate with ARC tools
The first step in aquiring a certificate is to create a certificate request. This is done using the grid-cert-request -int command. (The -int options means interactive usage). When issued, the tool will generate a certificate request and a private key. The tool will also ask for a password to protect the private key. Note, if the password is lost a new certificate must be obtained. The process is shown below:
First the private key is generated:
$ grid-cert-request -int A certificate request and private key is being created. You will be asked to enter a PEM pass phrase. This pass phrase is akin to your account password, and is used to protect your key file. If you forget your pass phrase, you will need to obtain a new certificate. Using configuration from /etc/grid-security/globus-user-ssl.conf Generating a 1024 bit RSA private key .....................................++++++ ....................++++++ writing new private key to '/home/jonas/.globus/userkey.pem'
To protect the private key from unauthorized access it is encrypted using a pass phrase. If this pass phrase is empty, anyone with access to your private key and certificate can gain access to the resources you have been granted. The pass phrase should also be different from your normal login password, so if your local system has been compromised the private key is still protected.:
----- You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- Level 0 Organization Name (do not modify) [Grid]: Level 1 Organization Name (do not modify) [NorduGrid]:
The following questions regards your affiliation domain and your email. It is important that your domain and the domain in the email address is the same.:
Your Domain [example.org]:mydomain.org Name (e.g., Hans Christian Andersen) []:Joe User Email address (e.g., h.c.andersen@example.org) []:joe.user@ mydomain.org
Finally the private key and a certificate request are generated.:
A private key and a certificate request has been generated with the subject: /O=Grid/O=NorduGrid/OU=mydomain.org/CN=Joe User/Email=joe.user@ mydomain.org If the CN=Joe User/Email=joe.user@mydomain.org is not appropriate, rerun this script with the -force -cn "Common Name" options. Your private key is stored in /home/joe/.globus/userkey.pem Your request is stored in /home/joe/.globus/usercert_request.pem Please e-mail the request to the NorduGrid Certification Authority ca@nbi.dk You may use a command similar to the following: cat /home/jonas/.globus/usercert_request.pem | mail ca@nbi.dk Only use the above if this machine can send AND receive e-mail. if not, please mail using some other method. Your certificate will be mailed to you within two working days. If you receive no response, contact NorduGrid Certification Authority at ca@nbi.dk
The result of the command are 3 files userkey.pem , usercert.pem and usercert_request.pem in a subdirectory called .globus in the user home directory. The userkey.pem your private key and should not be world readable. This can be achieved by using chmod 400 userkey.pem.
The contents of the usercert_request.pem should be sent by mail to you neareast Registration Authority (RA) by mail. The RA will verify your request and varify your identity. This can involve meeting with the RA and proving your identity with a passport or equivalent documents. The current list of RA:s can be found at the following page:
[http://ca.nordugrid.org/ra.html http://ca.nordugrid.org/ra.html]
Installing the grid certificate in your browser
When the signed certificate is received from the CA it has to be added to the usercert.pem file in the .globus directory.
The important parts of the mail are shown below::
-----BEGIN CERTIFICATE----- xasdj ... -----END CERTIFICATE-----
Copy the part shown above into the file usercert.pem in the .globus directory in your home directory.
Requesting a certificate using openssl
If neither the Terena Portal or the ARC tools are available you can use openssl directly to create a certificate request and a private key. Openssl will also ask for a password to protect the private key. Note, if the password is lost a new certificate must be obtained. The process is shown below:
$ mkdir -p ~/.globus $ openssl req -new -newkey rsa:2048 \ -out ~/.globus/usercert_request.pem \ -keyout ~/.globus/userkey.pem \ -subj "/O=Grid/O=NorduGrid/OU=nsc.liu.se/CN=Kalle Kula/emailAddress=kalle@nsc.liu.se"
Modify OU, CN and emailAddress as necessary. It is important that your OU and the domain in the email address is the same.
The result of the command are 2 files userkey.pem and usercert_request.pem in a subdirectory called .globus in your home directory. The userkey.pem is your private key and should not be world readable. This can be achieved by using chmod 400 ~/.globus/userkey.pem.
The contents of the usercert_request.pem should be sent by mail to you neareast Registration Authority (RA). The RA will verify your request and verify your identity. This can involve meeting with the RA and proving your identity with a passport or equivalent documents. The current list of RA:s can be found at the following page:
http://ca.nordugrid.org/ra.html
Installing the grid certificate in your browser
When the signed certificate is received from the CA it has to be put into the usercert.pem file in the .globus directory.
The important parts of the mail are shown below::
-----BEGIN CERTIFICATE----- xasdj ... -----END CERTIFICATE-----
Requesting membership in the SweGrid VO
To be able to use the SweGrid or Swestore resources a membership in the SweGrid VO and a corresponding group is required. To apply for membership, make sure that your certificate is installed in the browser. Then go to the following URL:
https://voms.ndgf.org:8443/voms/swegrid.se
and follow the instructions. In a couple of hours you will be added to the SweGrid VO.
To be added to the correct SNIC project send a mail to support@swegrid.se and specify your DN as shown in the Terena portal or from the arproxy --info command and which SNIC-project to be added to.
To be added to the correct Swestore allocation send a mail to swestore-support@snic.vr.se and specify your DN as shown in the Terena portal or from the arproxy --info command and which Swestore allocation to be added to.
Proxy certificates
Authentication on the grid is done by using special shortlived proxy certificates, which delegate authentication to specific resources. There are serveral tools available for creating, checking and destroying these proxy certificates.
ARC 1.0.x
Creating a proxy certificate
To create a shortlived proxy that can be used for authentication with grid services, the arcproxy command can be used. A 12 hour (default) proxy is created in the following example::
$ arcproxy Your identity: /O=Grid/O=NorduGrid/OU=lunarc.lu.se/CN=Jonas Lindemann Enter pass phrase for /home/jonas/.globus/userkey.pem: .++++++ .....++++++ Proxy generation succeeded Your proxy is valid until: 2011-03-11 03:00:14
The proxy file itself will be created in the /tmp directory with the format x509up_[uid], where uid is the userid number for your user account.
In some cases a longer lived proxy will be needed. This is achieved using the --constraint switch. A 24-hour can be created by issuing the following command:
$ arcproxy --constraint="validityPeriod=24H" Your identity: /O=Grid/O=NorduGrid/OU=lunarc.lu.se/CN=Jonas Lindemann Enter pass phrase for /home/jonas/.globus/userkey.pem: ....++++++ .....++++++ Proxy generation succeeded Your proxy is valid until: 2011-03-11 15:03:19
$ arcproxy Your identity: /O=Grid/O=NorduGrid/OU=lunarc.lu.se/CN=Jonas Lindemann Enter pass phrase for /home/jonas/.globus/userkey.pem: ................++++++ ......++++++ Proxy generation succeeded Your proxy is valid until: 2011-03-11 03:15:04
Checking proxy lifetime
The remaining lifetime of a proxy-certificate can be queried using the arcproxy command using the --info switch.
$ arcproxy --info Subject: /O=Grid/O=NorduGrid/OU=lunarc.lu.se/CN=Jonas Lindemann/CN=1567862803 Identity: /O=Grid/O=NorduGrid/OU=lunarc.lu.se/CN=Jonas Lindemann Time left for proxy: 11 hours 55 minutes Proxy path: /tmp/x509up_u500 Proxy type: X.509 Proxy Certificate Profile RFC compliant restricted proxy
Which shows that the proxy certificate is valid for 11 hours 59 minutes.
If a GSI proxy was generated the output would be:
$ arcproxy --info Subject: /O=Grid/O=NorduGrid/OU=lunarc.lu.se/CN=Jonas Lindemann/CN=proxy Identity: /O=Grid/O=NorduGrid/OU=lunarc.lu.se/CN=Jonas Lindemann Time left for proxy: 11 hours 54 minutes 57 seconds Proxy path: /tmp/x509up_u500 Proxy type: Legacy Globus impersonation proxy
Destroying a proxy certificate
A proxy can be destroyed with the -r or --remove switches.
$ arcproxy -r
or
$ arcproxy --remove
ARC 0.8.x
Creating a proxy certificate
To create a shortlived proxy that can be used for authentication with grid services, the grid-proxy-init command can be used. A 12 hour (default) proxy is created in the following example::
$ grid-proxy-init Your identity: /O=Grid/O=NorduGrid/OU=lunarc.lu.se/CN=Jonas Lindemann Enter GRID pass phrase for this identity: Creating proxy .................................................... Done Your proxy is valid until: Tue Jan 25 01:22:59 2011
The proxy file itself will be created in the /tmp directory with the format x509up_[uid], where uid is the userid number for your user account.
In some cases a longer lived proxy will be needed. This is achieved using the -valid switch. A 24-hour can be created by issuing the following command:
$ grid-proxy-init -valid 24:00 Your identity: /O=Grid/O=NorduGrid/OU=lunarc.lu.se/CN=Jonas Lindemann Enter GRID pass phrase for this identity: Creating proxy ................................................... Done Your proxy is valid until: Thu Feb 10 18:48:34 2011
Checking proxy lifetime
The remaining lifetime of a proxy-certificate can be queried using the grid-proxy-info command:
$ grid-proxy-info subject : /O=Grid/O=NorduGrid/OU=lunarc.lu.se/CN=Jonas Lindemann/CN=704530122 issuer : /O=Grid/O=NorduGrid/OU=lunarc.lu.se/CN=Jonas Lindemann identity : /O=Grid/O=NorduGrid/OU=lunarc.lu.se/CN=Jonas Lindemann type : RFC 3820 compliant impersonation proxy strength : 512 bits path : /tmp/x509up_u500 timeleft : 0:00:00
In this case the proxy has expired. Creating a new proxy-certificate with the grid-proxy-init command produces the following output from grid-proxy-info:
$ grid-proxy-info subject : /O=Grid/O=NorduGrid/OU=lunarc.lu.se/CN=Jonas Lindemann/CN=1908712807 issuer : /O=Grid/O=NorduGrid/OU=lunarc.lu.se/CN=Jonas Lindemann identity : /O=Grid/O=NorduGrid/OU=lunarc.lu.se/CN=Jonas Lindemann type : RFC 3820 compliant impersonation proxy strength : 512 bits path : /tmp/x509up_u500 timeleft : 11:59:55
Which shows that the proxy certificate is valid for 11 hours 59 minutes.
Destroying a proxy certificate
A proxy certificate can be destroyed using the grid-proxy-destroy command. This command will essentially just delete the temporary proxy file created with grid-proxy-init
VOMS certificates
To use the SweStore national storage resources a membership in a virtual organisation, VO, is required. When accessing the storage resources a special grid proxy certificate is required which indicates VO membership. The special proxy certificate requires that it is signed by the virtual organisation management server, VOMS. To enable this signing process, configuration files have to be added to the system. First a $HOME/.voms/vomses file with the following contents must be added:
"swegrid.se" "voms.ndgf.org" "15009" "/O=Grid/O=NorduGrid/CN=host/voms.ndgf.org" "swegrid.se"
Next the file /etc/grid-security/vomsdir/swegrid.se/voms.ndgf.org.lsc with the following contents:
/O=Grid/O=NorduGrid/CN=host/voms.ndgf.org /O=Grid/O=NorduGrid/CN=NorduGrid Certification Authority
Creating a VOMS proxy (ARC 0.8.x)
To create a proxy certificate the, voms-proxy-init, command is used. In the following example a voms proxy certificate is created with membership in the ops group.
$ voms-proxy-init -voms swegrid.se:/swegrid.se/ops Enter GRID pass phrase: Your identity: /O=Grid/O=NorduGrid/OU=lunarc.lu.se/CN=Jonas Lindemann Creating temporary proxy ............................................................. Done Contacting voms.ndgf.org:15009 [/O=Grid/O=NorduGrid/CN=host/voms.ndgf.org] "swegrid.se" Done Creating proxy .......................................................... Done Your proxy is valid until Thu Mar 10 23:14:57 2011
Creating a VOMS proxy (ARC 1.x)
VOMS proxies in ARC 1.x can be created using the arcproxy command and the -S or --voms switches as shown in the following example:
$ arcproxy -S swegrid.se:/swegrid.se/ops Your identity: /O=Grid/O=NorduGrid/OU=lunarc.lu.se/CN=Jonas Lindemann Enter pass phrase for /home/jonas/.globus/userkey.pem: .....++++++ ............++++++ Contacting VOMS server (named swegrid.se): voms.ndgf.org on port: 15009 Proxy generation succeeded Your proxy is valid until: 2011-03-10 23:33:06